IT Staffing Strategies for Compliance-Heavy Industries in 2025
November 18, 2025
Go back to "News & Updates"

If you work in a heavily regulated space—healthcare, finance, insurance, government, energy, critical infrastructure—you’re likely feeling the squeeze from both sides in 2025:
- Regulations keep multiplying (data privacy, AI rules, cyber incident reporting).
- Skilled IT and security talent is still hard to find and even harder to keep.
The question isn’t just “How do we hire more people?” It’s: How do we design IT staffing so we actually stay compliant and secure?
This article walks through practical IT staffing strategies tailored for compliance-heavy industries in 2025.
1. Know the 2025 compliance landscape you’re hiring into
Before you build a team, you need to understand the world they’re walking into. In 2025, a few trends are shaping IT and security staffing:
- Stricter data protection & privacy rules – Regulations are tightening around data encryption, cross-border data transfers, vendor risk, and breach notification timelines.
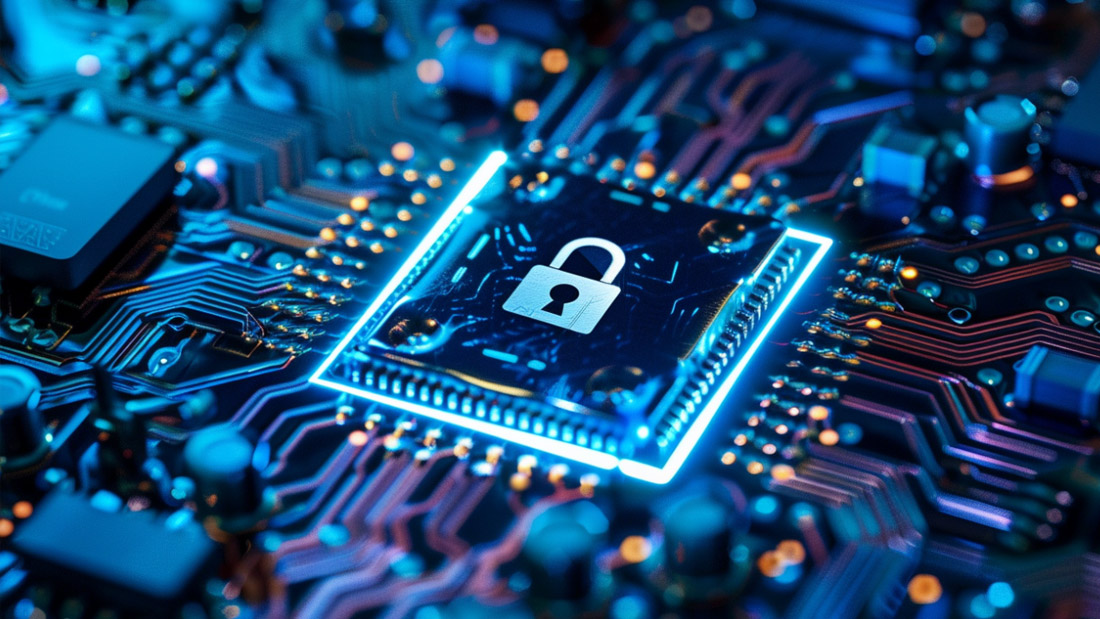
- Cyber incidents are more frequent and more regulated – Governments and regulators increasingly require fast disclosure of cyber incidents and more detailed reporting.
- AI and “AI compliance” are now real staffing needs – Companies are expected to govern how they use AI, including fairness, transparency, explainability, and data usage.
- Cybersecurity and AI talent is in high demand – Cybersecurity and AI/ML roles remain some of the fastest-growing tech positions, creating a real skills shortage.
Your IT staffing strategy has to respond to this: you’re not just filling “IT” roles; you’re filling regulatory survival roles.
2. Start with principles: what a compliant IT team needs to be
Regardless of your industry, a compliance-ready IT function should be:
- Interdisciplinary – Compliance doesn’t live only in Legal or IT. Your IT team needs to work hand-in-hand with legal, risk, audit, and operations.
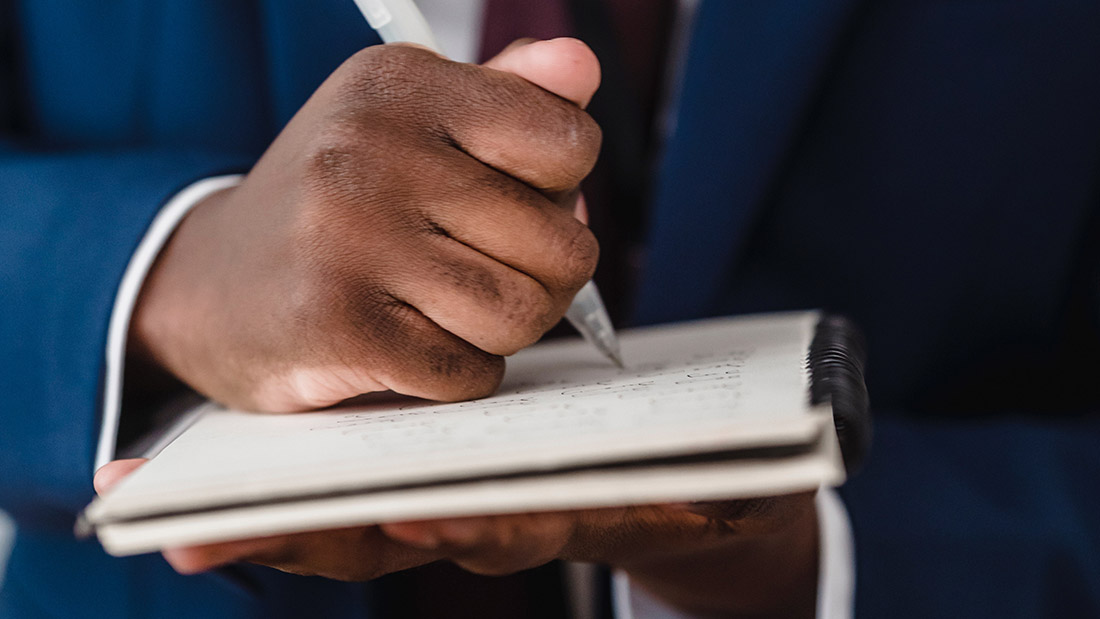
- Document-driven – If it’s not documented, regulators assume it didn’t happen. Your staffing model must cover policy writing, procedural docs, change logs, test evidence, and incident records.
- Audit-ready by default – Staff must be used to working in a world where access is logged, changes are traceable, and decisions are explainable.
- Continuous-learning oriented – Regulations, tools, and threats evolve constantly, so your people can’t be “one-and-done” trained.
Use these as a filter for every hire and every staffing decision.
3. Design roles around compliance, not just tech
Instead of generic job descriptions like “Senior Sysadmin,” design compliance-aware roles. Some examples for 2025:
a) Security & compliance core
- Information Security Engineer / Architect – Owns secure configurations, hardening standards, and monitoring aligned with frameworks like NIST, ISO 27001, PCI DSS, HIPAA, etc.
- GRC (Governance, Risk & Compliance) Engineer / Analyst – Bridges IT and audit, maps controls to regulations, runs risk assessments, and helps prepare for certifications and audits.
- Cloud Security Engineer – Focuses on secure setups in AWS/Azure/GCP: identity and access, encryption, logging, and compliance with industry rules.
b) Data, privacy, and AI
- Data Protection / Privacy Engineer – Works with the DPO or privacy team to implement privacy-by-design, data minimization, and retention rules in actual systems.
- AI Governance / AI Compliance Specialist – Evaluates AI tools, sets usage policies, and ensures AI systems respect relevant regulations and internal governance frameworks.
- Data Engineer with regulatory expertise – Designs pipelines so sensitive data is masked, tokenized, or pseudonymized where required.
c) Cyber defense and incident response
- SOC Analysts / Threat Hunters – Monitor for threats, coordinate response actions, and ensure incident handling follows regulatory protocols.
- Digital Forensics & Incident Response (DFIR) Lead – Ensures that evidence is collected and preserved properly for both internal learning and any regulatory investigations.
You may not need all of these full-time in-house, but you do need clear ownership of these responsibilities across employees, contractors, and vendors.
4. Balance in-house, managed services, and specialized partners
For compliance-heavy industries, the best approach is usually a hybrid staffing model:
Keep these mostly in-house
- Security leadership – CISO, Head of Security, or equivalent.
- Key access and identity management roles – the people who control “who can access what.”
- Core compliance program owners – the ones defining policies and risk appetite.
This ensures you maintain direct control over the most sensitive levers of compliance.
Consider managed services for
- 24/7 SOC and monitoring.
- Penetration testing and red teaming.
- Specialized audits and certifications (e.g., PCI DSS, SOC 2).
External partners can bring niche expertise you might not be able to hire or retain full-time, while still working within your compliance framework.
Use nearshoring/offshoring carefully
- Check data residency and data transfer laws before sending work or data abroad.
- Ensure contracts include clear security and compliance obligations.
- Verify that offshore teams follow your access control, logging, and incident response rules.
5. Bake compliance into your hiring and onboarding process
a) Hire for mindset as much as skill
In interviews, look for:
- Comfort working with policies and documentation.
- Experience in regulated industries (finance, healthcare, critical infrastructure, etc.).
- Healthy attitude toward controls—seeing them as guardrails, not bureaucracy.
Ask scenario questions like: “Tell me about a time a security or compliance control slowed you down. What did you do?”
You want people who solve problems within the rules, not by bypassing them.
b) Make compliance a formal part of onboarding
- Short training on relevant regulations (HIPAA/PCI/GDPR/etc., depending on your sector).
- Clear explanation of what gets logged, what must be documented, and how to handle incidents.
- A checklist tied to their role: what they must do to keep their work compliant.
c) Align performance reviews with compliance behavior
- Reward clean change histories and proactive documentation.
- Recognize people who catch and report issues early.
- Avoid KPIs that only measure speed or volume and ignore compliance.
If your KPIs ignore compliance, your staff will too.
6. Use automation and AI—with governance
In 2025, a lot of IT and compliance work can be assisted or accelerated with AI and automation:
- Automated log analysis and anomaly detection.
- AI-assisted policy drafting and evidence collection.
- AI tools to support threat hunting and incident triage.
But every AI tool you adopt creates new compliance questions:
- Where does the data go?
- Who can see or train on it?
- Can you explain the model’s decisions to regulators?
That’s why you need AI-literate staff who can:
- Evaluate tools before adoption.
- Configure them with privacy and security in mind.
- Document how they’re used and what data they touch.
Think of AI as a force multiplier for your staff—not a replacement for compliance expertise.
7. Invest heavily in upskilling and internal mobility
Given the talent shortage, one of your best IT staffing strategies in 2025 is to build your own experts.
Practical ideas:
- Certification paths for security, cloud, and compliance (CISSP, CISM, CCSP, CISA, privacy certs, etc.).
- Cross-training between IT and compliance/legal through internal workshops.
- Rotational programs where promising IT staff spend 6–12 months in a security or GRC role.
Make it clear: If you want a future here, learning security and compliance is a big career advantage.
That message alone can shape how your staff invest their time.
8. Create small, cross-functional “compliance pods”
Instead of isolating compliance in one department, create pods for high-risk areas such as:
- Core banking or financial systems.
- EHR/PHI platforms in healthcare.
- Payment and billing systems.
- Critical infrastructure control systems.
Each pod might include:
- 1–2 engineers (application or infrastructure).
- 1 security engineer.
- 1 GRC or compliance lead.
- A business owner or product manager.
They jointly own:
- Risk assessments for that system.
- Security and privacy controls.
- Change approval and documentation.
- Incident playbooks.
This structure makes compliance operational, not theoretical.
9. A simple 2025 checklist for IT leaders in regulated industries
If you’re a CIO, CISO, or IT director in a compliance-heavy industry, here’s a straightforward action list:
- Map your regulations – List every major regulation/framework that touches your tech stack (HIPAA, PCI DSS, SOX, GDPR, local cyber laws, AI regs, etc.).
- Map regulations to responsibilities – For each requirement, answer: “Which role or person owns this in practice?” Fill gaps with new roles or vendor support.
- Redesign key roles – Update job descriptions for IT, data, and security roles to explicitly include compliance responsibilities and documentation.
- Decide what must stay in-house – Especially access management, policy governance, and incident decision-making.
- Structure your vendor model – Choose where to use managed services, nearshore teams, and specialized consultancies—and wrap them in clear, enforceable contracts.
- Build a training and certification plan – Budget for ongoing training. Make it normal, not “nice to have.”
- Review AI and automation usage – Inventory tools, check data flows, and assign AI governance responsibilities.
- Stress-test your incident response – Run at least one tabletop exercise with IT, legal, and compliance to see if your staffing model stands up under pressure.
Final thoughts
In 2025, compliance-heavy industries don’t just need “more IT people.” They need the right mix of skills, roles, partners, and processes that can stand up to regulators and real-world threats.
If you design roles around regulations, mix in-house talent with specialized partners wisely, invest in upskilling, and put AI under proper governance, you’ll end up with an IT staffing model that keeps your organization compliant, resilient, and ready for whatever comes next.